✍️ Author’s Note – My Journey Into Cybersecurity
As a developer, learning the core concepts of cybersecurity was an eye-opener for me.
Some practices I followed unknowingly. Others, I applied out of obligation — without really connecting to the why.
But once I started preparing for the CISSP, it all began to click.
I finally understood why we follow certain principles, why security needs to be baked into design, and why risk thinking matters.
To make sense of it all — and to share it in a way that feels real — I created Aanya.
She’s a developer, just like many of us. Through her eyes and her journey, I bring my own learnings to life — with stories, diagrams, analogies, and a lot of curiosity.
This is not just about passing an exam.
It’s about building secure systems that make sense — from the ground up.
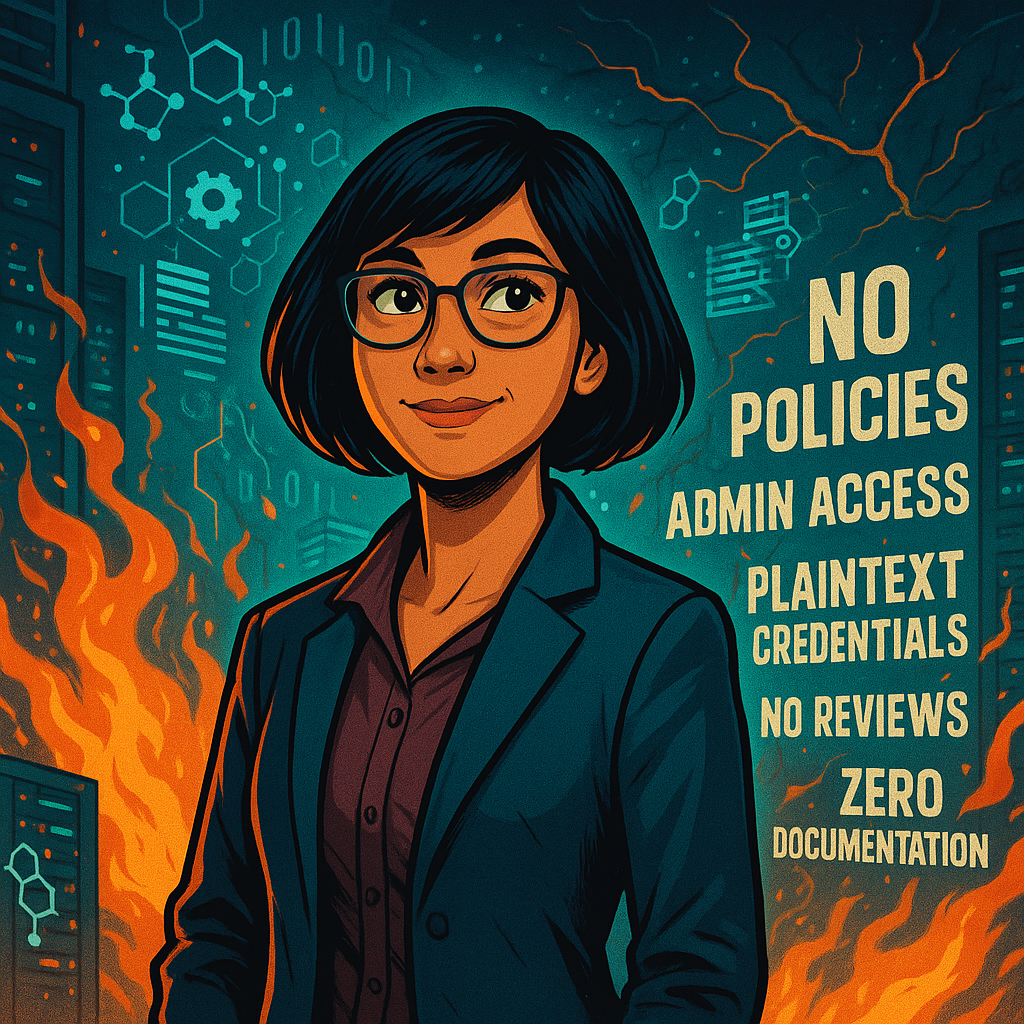
🎯Introducing Aanya !
Aanya is a curious mind with solid tech confidence. She’s not your average engineer.
She’s the one you call when things are on fire.
With 15 years in tech and development on Java. Python. Cloud. DevOps.
From high-frequency trading systems, retail , fintech to healthcare platforms to government-scale backend beasts —
If it’s complex, Aanya has built it, broken it, tested it, and scaled it.

She’s seen bugs no one could find, fixed infra no one understood, and led teams that forgot what sleep was.
Now, She wants to build resilience.
She wants to understand where systems break when no one’s watching.
She wants to fight the chaos that lives between the lines of production code.
🧭 Enter: Neuromesh
A shiny, fast-growing startup with big ideas and even bigger investor decks.
AI. Automation. Scalable architecture.
They promised freedom, speed, and a “no red tape” engineering culture.
Aanya joined as their first senior technical lead.Day 1 was supposed to be onboarding.Instead, she walked straight into a firestorm.
🔥 What She Saw
No policies.
No controls.
No one in charge of anything.
🚪 Everyone had admin access
📦 Production credentials in plaintext in code repos
🚀 Engineers pushing directly to prod — no reviews, no rollbacks
🚨 No incident response playbook — because apparently “they never had an incident”
📜 Zero compliance. Zero documentation. Zero accountability.
It wasn’t a startup.
It was a security time bomb.
🤯 “They Don’t Know What They Don’t Know”
She saw the cracks. She heard the silence. And she made a quiet but clear decision:
“I’m not going to lecture them.I’m going to show them.One problem at a time.”
👉 She would use the principles of one of the most respected security practises in the world — ISC²’s CISSP — to bring change.
She began mapping every mess to a principle.
She borrowed from CISSP, NIST, OWASP etc — not for certification, but for structure.
She thought like an architect, a defender, a strategist.
Through her eyes, this series will explore how CISSP principles can transform an organization’s security posture — one domain at a time.
