⬅️ Missed the beginning?
👉 Start with Chapter 1: Meet Aanya and Discover What CISSP Is
At Neuromesh the fast-paced workstyle often made it difficult to understand who was responsible for what. Aanya could observe the gaps but she still wondered
Where to get started ?
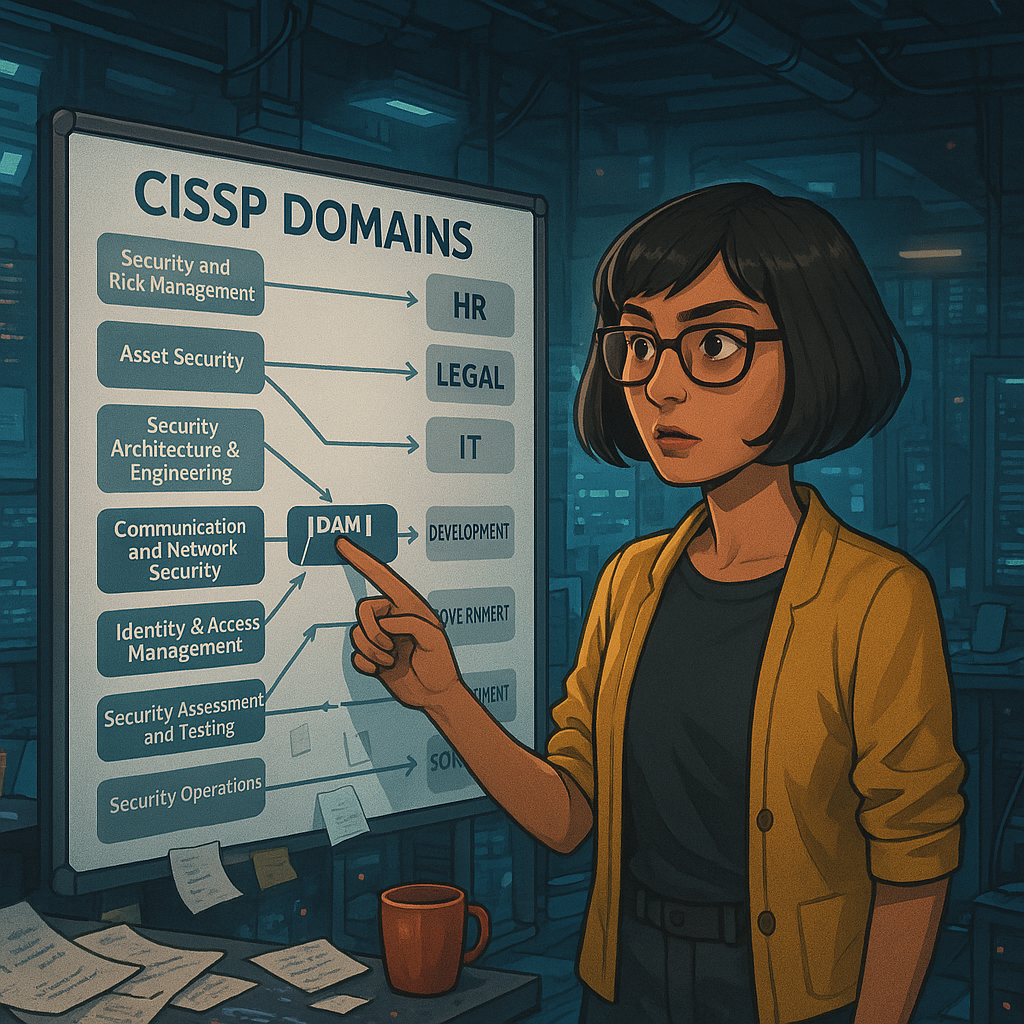
She found her answer in the CISSP domains — eight broad areas defined by ISC² that map out the full spectrum of cybersecurity knowledge.
There was a mental model it offered.
“This feels like a system I can study — not just react to.”
🧠 What Each Domain Helped Her Understand
As she explored each domain, she found herself asking better questions.
Not “what’s wrong here?” — but “what kind of problem is this?”
Here’s how she started mapping them:
🛡️ CISSP Domain : 1. Security & Risk Management
Aanya realized this domain is about who’s responsible, and how risk is defined and managed.
💡 What It Helped Aanya Learn :
Do we have security policies? Who approves them?
Are we aligned with a governance model (like COBIT)?
What is our threat landscape?
Do we assess inherent vs residual risk?
How do we balance security goals with business priorities?
💡 In this domain, we will explore:
Risk analysis methods: qualitative vs quantitative
Risk treatment: avoid, mitigate, transfer, accept
Security roles & responsibilities (like data owner, custodian)
Ethics and professional conduct (from ISC² Code of Ethics)
Compliance & legal frameworks: GDPR, SOX, HIPAA
🔐 This domain trains our strategic lens — to think like a risk-aware leader, not just a technician.
🛡️ CISSP Domain : 2. Asset Security
This domain gave Aanya a deceptively simple but powerful insight:
📦Before you protect anything, you have to know what you have.
💡 What It Helped Aanya Learn :
She learned to think about:
Asset identification — not just laptops and servers, but databases, documents
Data classification — public, internal, confidential, restricted
Who owns the data? How is it labeled? Where is it stored?
What retention, backup, and disposal policies exist?
💡 Key topics:
Data lifecycle management
Privacy vs confidentiality
Asset handling procedures (especially for removable media and cloud backups)
Regulatory requirements around PII and sensitive data
📌 This domain teaches data stewardship — a crucial mindset when every employee is a potential data creator or risk vector.
🛡️ CISSP Domain : 3. Security Architecture & Engineering
🏗️ Secure by design, not by accident.
She started asking: Do we follow any security design principles like least privilege, defence in depth?
Are we using strong crypto — or just whatever’s default?
How is trust established between components?
What are the known system vulnerabilities?
💡 We will learn:
Architectural patterns (e.g., ring models, security zones)
Cryptographic basics: symmetric vs asymmetric, hashing, key management
Threat modeling
Cloud security shared responsibility model
Vulnerabilities in hardware, firmware, and operating systems
🔐 This domain trains you to engineer trust into your infrastructure — instead of bolting it on.
🛡️ CISSP Domain : 4. Communication & Network Security
📡 Because insecure networks are the fastest breach vectors.
This domain helped Aanya understand how systems communicate, and how that communication needs to be controlled, encrypted, and segmented.
She began observing:
Do internal services use encryption?
Are networks segmented between dev, test, prod?
Is VPN access too open?
💡 Core concepts:
Secure network design (firewalls, proxies, VLANs)
Network protocols (TLS, SSH, IPsec)
Remote access & VPN security
Network monitoring and detection tools
📌 This is where packet meets policy — and your defences start (or fail) at the perimeter.
🛡️ CISSP Domain : 5. Identity and Access Management (IAM)
🔐 The front door. The side doors. All the doors.
She started asking:
Who has access to what?
Are permissions aligned to roles or manually assigned?
How do we offboard people?
💡 You’ll learn:
Authentication factors (something you know/have/are)
Identity lifecycle management (provisioning, revocation)
Single Sign-On (SSO), Federated Identity, IDaaS
Access control models (RBAC, ABAC, MAC, DAC)
📌 IAM is often the first real control in any system.
🛡️ CISSP Domain : 6. Security Assessment & Testing
🔍 If you don’t measure it, you don’t know if it works.
She asked:
How do we know our systems are secure?
When was the last vulnerability scan?
Do we do penetration testing?
💡 You’ll learn:
Vulnerability scanning, penetration testing
Code review and static/dynamic testing
Security audits and assessments
KPIs, metrics, and continuous monitoring
📌 Testing doesn’t just reveal gaps — it proves whether controls are working.
🛡️ CISSP Domain : 7. Security Operations
📊 Real-time defence, ongoing vigilance.
This domain exposed the heartbeat of security: monitoring, detection, and incident response.
Aanya began to wonder:
Are there logs?
Who watches them?
What happens if someone clicks a malicious link?
Do we have an incident response plan?
💡 You’ll explore:
Security Information & Event Management (SIEM)
Forensics and digital investigation basics
Incident response lifecycle
Business Continuity & Disaster Recovery (BC/DR)
🔐 This is where alerts become action — and where silence can be fatal.
🛡️ CISSP Domain : 8. Software Development Security
💻 Securing what we build — from commit to prod.
She learned to look for:
Are secrets hardcoded ?
Is there peer review?
Are there security gates in CI/CD?
💡 Topics covered:
Secure SDLC phases
Threat modeling
Code review best practices
OWASP Top 10
DevSecOps integration
📌 Code moves fast — but secure code has checkpoints, not just speed bumps.
🔜 Upcoming Next: IAM - Identity and Access Management
“Access is the one control that every team, every tool, every environment touches.”
From code repositories to CI/CD pipelines, databases to SaaS dashboards
And this was the first thing she saw in her assignment as a Developer that accesses were not granted with scrutiny or following any particular reasoning.
So she started learning by reading about :
What is Identification , Authentication , Authorization ?
What exactly are different Access Models ?
What are different Access Controls ?
What kind of situations can arise if there is possibility of an attack in different Access Mechanisms?
Follow Aanya’s Journey and learn along with her.
