🎯 Concept Focus: CIA, Authenticity, and the DAD–MOM Equation
The CIA Triad: Security’s Core Commitments
Before you roll out firewalls or encrypt databases, ask: What exactly am I trying to protect?
Answer: Confidentiality, Integrity, and Availability. Known as the CIA Triad, these are not buzzwords. They're strategic goals for any security initiative — whether you’re hardening a hospital’s patient record system or managing access to a banking platform.
Let’s break them down:
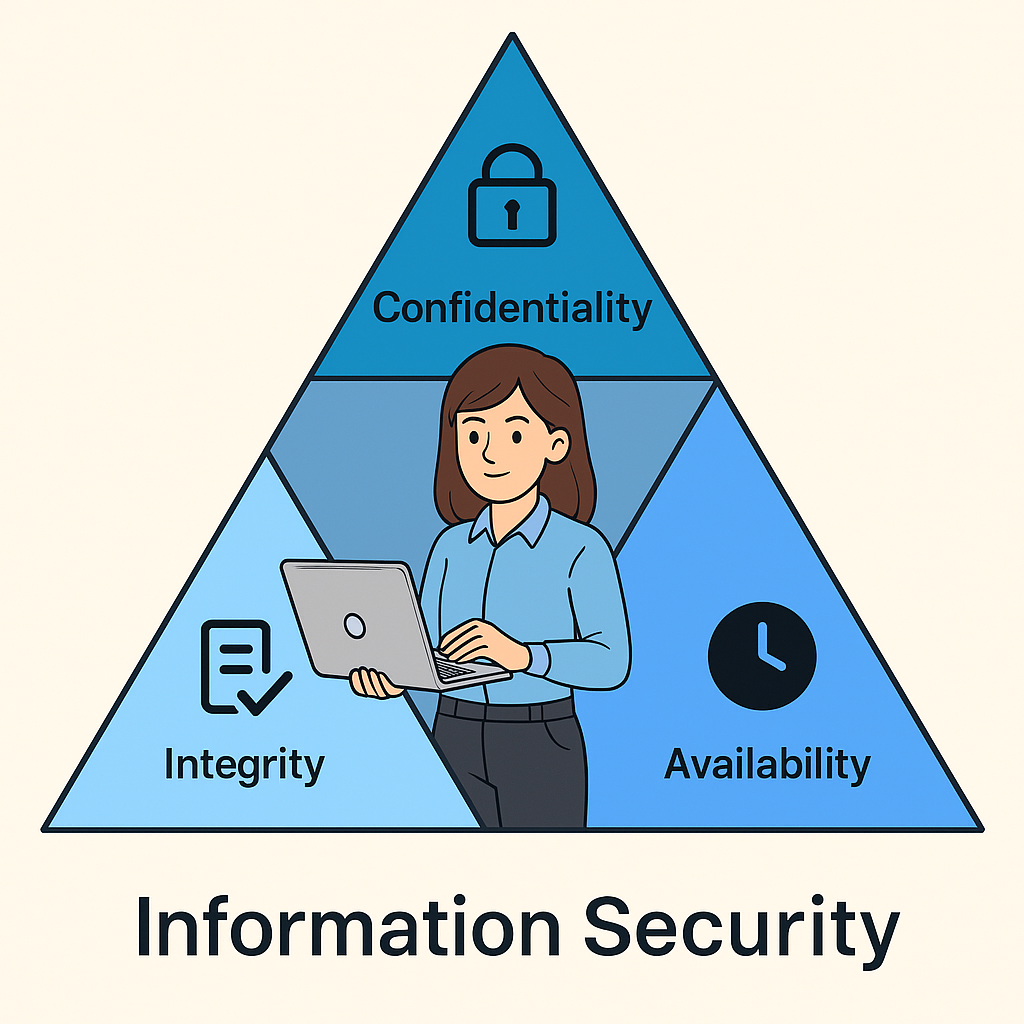
Confidentiality → Preventing Disclosure
Confidentiality ensures that information is only seen by those authorized to access it. It's about controlling exposure, both internal and external.
Controls to enforce confidentiality:
Access Controls (physical & logical): Badge readers, login prompts, ACLs.
Encryption:
At Rest: Full-disk encryption (e.g., BitLocker, LUKS).
In Transit: TLS, VPN tunnels, SSH.
Least Privilege: Users only get access to what their role demands.
Need-to-Know: Restricts access to specific classified objects (e.g., HR payroll files).
Threat examples:
Business email compromise: Finance team misled into sharing client invoices.
Unsecured cloud storage: S3 buckets publicly exposed due to misconfiguration.
Lost laptop with sensitive data: No disk encryption → data leakage risk.
Phishing with QR codes: Users scanned malicious codes in printed flyers.
Internal misuse: Junior analysts snooping on executive compensation data.
Integrity → Preventing Unauthorized Alteration
Integrity means data remains accurate, consistent, and trustworthy — from creation to destruction.
Imagine if an employee’s salary was altered without audit logs — that’s an integrity breach.
Controls to enforce integrity:
Hashing: SHA-256 checksums to detect tampering.
Digital Signatures: Prove source + integrity of signed data.
Change Control: No production change without approvals.
Separation of Duties: Developers can't directly deploy to prod.
Immutable Logs: Centralized and tamper-resistant event logs.
Threat examples:
Man-in-the-middle on internal API: Alters JSON payloads before reaching database.
Firmware updates from unofficial sources: Inject malicious code into routers.
Developer alters audit trail to cover unauthorized query.
Database errors caused by misconfigured ETL pipeline.
Automated financial reports misstate revenue due to unchecked formula change.
Availability → Preventing Destruction or Downtime
Availability means users get what they need, when they need it — reliably and without obstruction.
It’s not just a server’s uptime. It’s about resilience under attack, recovery after disaster, and continuity through chaos.
Controls to ensure availability:
Backup & Restore Plans: Tested, versioned, offsite backups.
RAID Configurations: Disk-level redundancy.
High Availability (HA) Architectures: Load balancers, failover clusters.
DDoS Protection: Scrubbing services and rate limiting.
Business Continuity Planning (BCP): How operations resume post-disaster.
Threat examples:
Ransomware encrypting production systems without backup access.
Cloud misconfiguration deletes production VMs due to lack of approval workflow.
Power outage in primary data center with no failover.
Flooded server room in on-prem HR office without offsite backup.
Botnet DDoS on DNS provider, taking customer portal offline.
Authenticity & Non-Repudiation — Trust and Accountability
Sometimes, it's not just about what happened — but who did it, and whether they can deny it later.
Authenticity ensures that you're really talking to who you think you're talking to — whether it's a human or a system.
e.g., A smartcard and PIN to access a nuclear control console.
Non-repudiation ensures actions are logged in a way that the actor can't later deny them.
e.g., A digitally signed purchase order backed by secure logs.
Together, these build accountability — essential for audits, investigations, and zero-trust design.
🎯 Concept Focus: Security Governance
What Is Security Governance?
Security Governance refers to the policies, procedures, roles, and responsibilities an organization uses to make informed security decisions. Its core purpose is to reduce risk to an acceptable level while ensuring that security supports business strategy, not operates in isolation.
Security Governance is one part of GRC:
GRC → Governance → Risk Management → Compliance
Security Governance ensures that:
The security program aligns with the business mission and goals.
Risk is identified and managed.
Resources are used responsibly
Due Care and Due Diligence standards are met
Vision Defines what the company aspires to become.
Mission Describes the company’s function and purpose — what it is and why it exists.
Goals Organizational aims that contribute to the mission.
Objectives Specific, short-term milestones that support goals.
Strategy Actions taken to accomplish objectives and fulfil the mission.
Tactical Translating strategy into medium-term departmental plans.
Operational Day-to-day actions that implement tactics.
Security Governance Components
Risk Assessment → Identify, evaluate, and prioritize risks
Roles and Responsibilities →Define accountability for each function
Information Security Program →Select framework and define policies, procedures
Security Management (Tactical) →Convert policies into actionable plans
Security Operations →Implement, monitor, detect, recover, audit, update
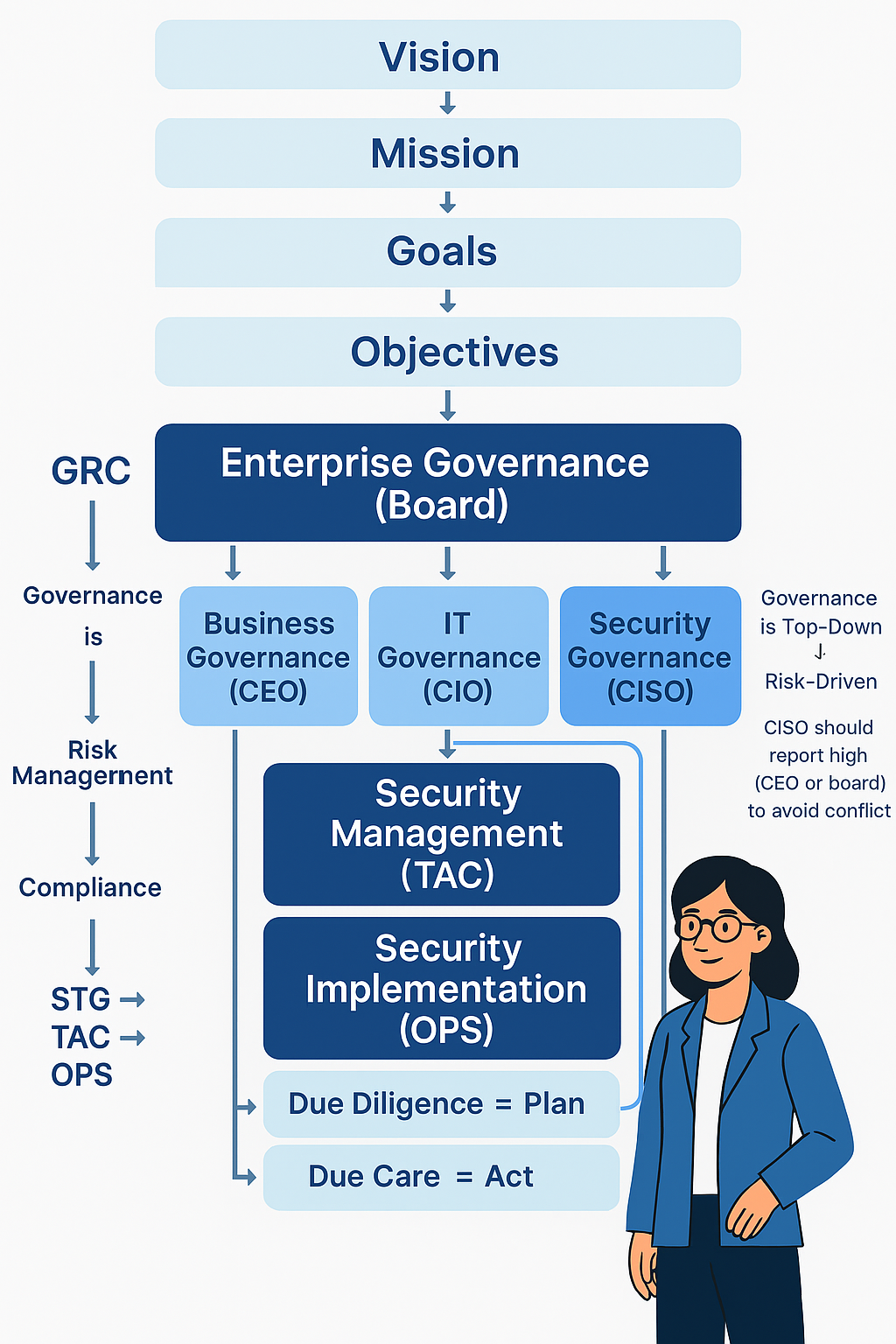
Due Diligence vs. Due Care
TermDefinitionDue DiligenceThe discovery phase: identifying risks, analyzing threats, evaluating options.Due CareThe action phase: implementing safeguards based on identified risks.
🔍 Due Diligence = "Thinking before doing"
🛠️ Due Care = "Doing the right thing once you know"
Example from your notes:
Due Diligence: A CISO reviews cloud provider compliance.
Due Care: Based on that, the company enables MFA, updates policy, and trains staff.
We will continue with Governance details and Compliance etc in next Articles
🧠 Brain Ticklers
Q1: Anya was reviewing an incident where a system outage prevented Neuromesh’s HR team from accessing payroll data just before monthly disbursements. Investigation showed a single point of failure on a misconfigured server.
What element of the CIA triad was primarily violated?
A. Confidentiality
B. Authenticity
C. Availability
D. Integrity
Q2:Neuromesh’s CISO, Marcus, evaluates a new third-party endpoint security solution. After a full vendor risk assessment, the team approves it. Anya is then asked to implement multi-factor authentication, configure endpoint agents, and deploy training.
Which action represents Due Diligence, and which represents Due Care?
A. Evaluating the vendor is due care; implementing MFA is due diligence
B. Performing vendor risk assessment is due diligence; implementing controls is due care
C. Training employees is due diligence; vendor research is due care
D. Both actions are examples of due care
Q3:Leila, Neuromesh’s IAM specialist, is drafting new access control policies for developers and contractors. These policies are based on a recently approved zero-trust strategy signed off by Marcus and the CIO.
Leila’s work is best classified under which governance tier?
A. Strategic
B. Operational
C. Tactical
D. Executive
Q4:Marcus, Neuromesh’s CISO, currently reports to the CIO. However, he notices frequent conflicts — like security priorities being overridden by IT budget constraints. He recommends reporting to the CEO instead.
What’s the primary reason for this change?
A. To improve IT governance visibility
B. To gain access to more infrastructure budgets
C. To reduce conflict of interest and strengthen security independence
D. To streamline patch management and IT operations
Q6: An attacker exploits a SQL injection vulnerability in Neuromesh’s internal financial portal. They modify invoice values and insert fake transactions into the system.
According to the DAD framework, which part of CIA has been compromised?
A. Confidentiality
B. Integrity
C. Availability
D. Authenticity
This episode of Anya in Cybersecurity covers Security & Risk Management — part of CISSP Domain 1 preparation. Follow the full series for structured exam readiness.
