🎯 Concept Focus
When people hear “compliance,” they often think it is security.
It isn’t.
Compliance is a baseline — the minimum set of actions, controls, and reporting an organization must meet to satisfy laws, regulations, and industry standards. It’s about staying out of legal hot water and avoiding penalties.
Security governance, on the other hand, sets the direction — aligning policies, risk appetite, and investments with business goals. You can tick every compliance box and still be vulnerable if your governance or technical defences are weak.
Today, we’ll explore three pillars that often intersect:
Intellectual Property Protection — safeguarding creations of the mind.
Compliance Frameworks & Standards — the rulebooks that dictate how we measure and prove our security posture.
Professional Ethics — the human compass for decision-making.
Intellectual Property in the Security Context
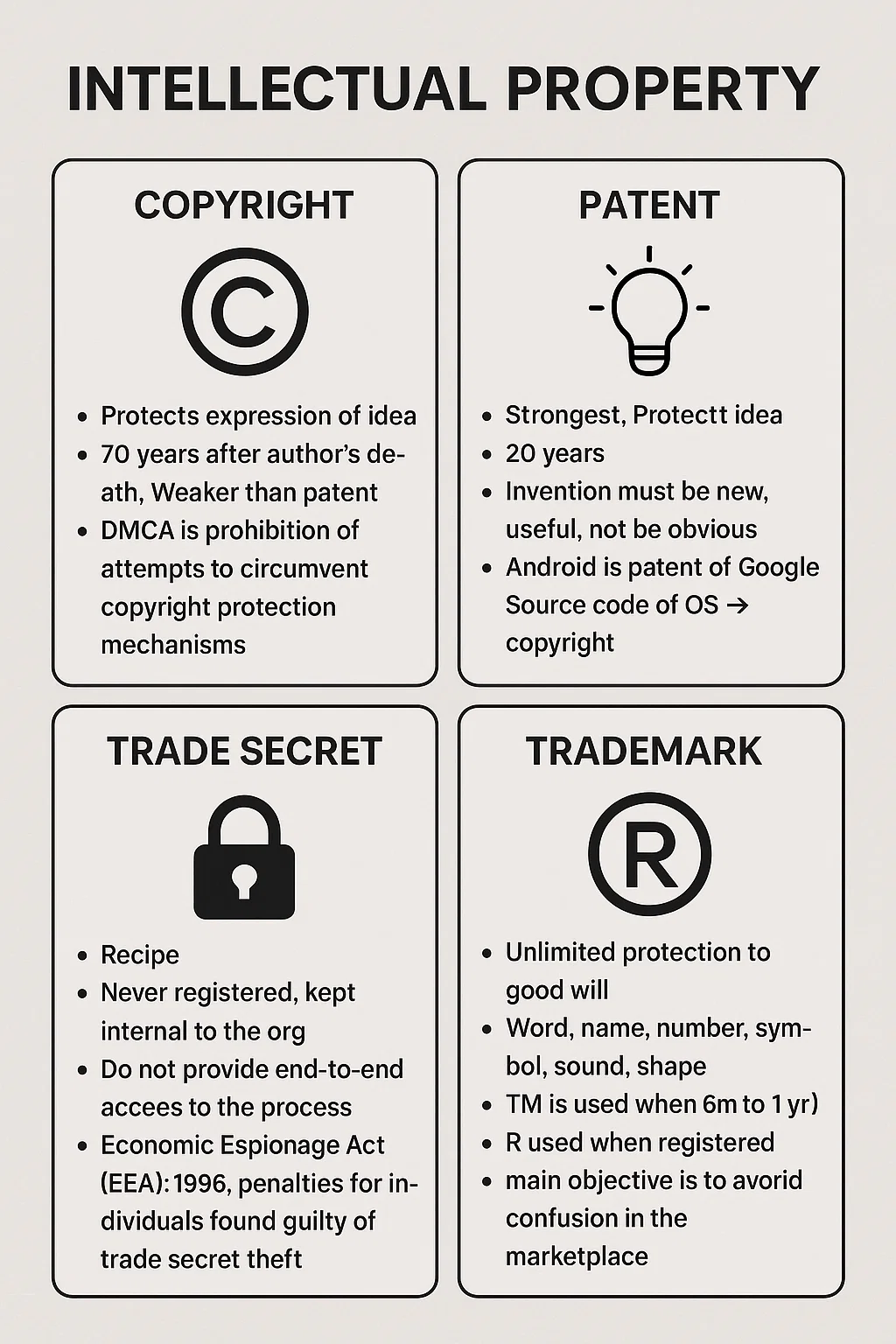
Copyright
Protects the expression of an idea — like source code, documentation, or a logo design.
Duration: typically 70 years after the author’s death.
Limitation: Doesn’t protect the underlying idea — someone can reimplement it differently.
Example: The Neuromesh API docs are copyrighted, but if someone rewrites them in their own words, copyright law may not apply.
Patent
Protects the idea itself if it’s novel, useful, and non-obvious.
Duration: 20 years from filing.
Stronger than copyright.
Example: A proprietary machine-learning algorithm for fraud detection could be patented.
Trade Secret
Protects valuable, confidential information not publicly disclosed.
Duration: indefinite — as long as secrecy is maintained.
Example: The exact configuration settings for Neuromesh’s anomaly detection system.
Law: Economic Espionage Act (1996) in the US criminalizes theft.
Trademark
Protects identifiers like names, symbols, sounds, and shapes that distinguish goods or services.
Duration: unlimited with proper renewal.
Example: The Neuromesh hexagon logo.
Purpose: Avoids confusion in the marketplace.
Key Insight:
Source code could be covered by copyright and treated as a trade secret — giving you a legal wall and a locked vault.
Digital Rights, Import/Export Controls
Digital Rights Management (DRM)
Technology to control how digital content is used — from preventing Netflix downloads to restricting eBook printing. DRM often works alongside Data Loss Prevention (DLP) tools.
Export/Import Restrictions
ITAR (US): Controls defense-related exports.
EAR (US): Controls commercial dual-use tech.
Wassenaar Arrangement: International agreement to control dual-use goods like encryption tools, drones, and GPS systems.
Some countries require encryption imports to hand over private keys to authorities.
Compliance Frameworks vs Standards
Frameworks = flexible structures for organizing controls.
Examples: COSO, ITIL, COBIT, NIST Cybersecurity Framework, ISO 27000 Series.
Used to align with business objectives, adapt to context.
Standards = fixed benchmarks for measuring compliance.
Examples: ISO 27001, PCI DSS.
Mandatory, often certification-based.
Global Regulations (highlights):
GDPR (EU): Data protection for EU residents/citizens, inside or outside EU.
HIPAA (US): Protects medical records; requires Business Associate Agreements (BAAs).
GLBA (US): Safeguards consumer financial info.
SOX (US): Prevents corporate accounting fraud.
CCPA (California): Gives consumers control over personal data.
FISMA/FedRAMP (US): Federal info security and cloud provider compliance.
POPIA (South Africa): Protects personal information across public/private sectors.
Industry-Specific:
PCI DSS: Cardholder data protection in payment processing.
Major Global Regulations In Detail
GDPR : Read more about GDPR here
HIPAA: Read more about HIPAA here
Professional Ethics: The PAPA Framework
The PAPA model (Protect, Act, Provide, Advance) outlines the ethical responsibilities of security professionals at both the individual and enterprise levels. These aren’t just aspirational ideals — they’re practical, enforceable standards that influence daily decisions, incident responses, and long-term professional conduct.
1️⃣ P — Protect (Individual Perspective)
A security professional’s first obligation is to safeguard the public good, uphold trust in information systems, and maintain the integrity of shared infrastructure.
Key Commitments:
Preserve public trust – handle sensitive information in ways that build confidence among users, customers, and stakeholders.
Promote security awareness – advocate for sensible, effective security practices without resorting to fearmongering.
Protect public infrastructure – from the internet backbone to cloud platforms, treat shared resources as critical assets.
Discourage unsafe practices – speak up against shortcuts, negligence, or intentional policy violations.
Example: If Neuromesh developers propose bypassing encryption “just for testing,” Anya must flag it — even if it’s faster — because the public’s trust in their product is at stake.
2️⃣ A — Act (Individual Perspective)
Ethical action means behaving with honesty, fairness, responsibility, and legal compliance, even under pressure.
Key Commitments:
Be truthful and transparent – inform stakeholders promptly about actions or incidents that affect them.
Honor agreements – follow both explicit contracts and implied commitments.
Prioritize fairly – in conflict resolution, place public safety first, followed by duty to your organization, individuals, and the profession.
Provide prudent advice – avoid exaggerating threats or offering false reassurance.
Operate within your competence – only take on work you’re qualified to perform.
Handle jurisdiction conflicts wisely – when laws differ, apply the rules of the jurisdiction where the service is rendered.
Example: If Neuromesh detects a vulnerability in a client’s system, Marcus must report it accurately and promptly — even if the client might be embarrassed or financially impacted — because concealing it would be unethical and potentially illegal.
3️⃣ P — Provide (Enterprise Perspective)
Organizations have a duty to deliver secure, reliable, and competent service to their customers, partners, and stakeholders.
Key Commitments:
Protect asset value – ensure systems, applications, and data retain their integrity, availability, and confidentiality.
Respect client trust – handle privileged access with discretion.
Avoid conflicts of interest – decline activities that could compromise objectivity or loyalty.
Operate within capability – take on engagements only if the organization has the expertise and resources to deliver securely.
Example: If Neuromesh is asked to deploy a healthcare analytics platform but lacks HIPAA-compliant infrastructure, leadership must either upgrade systems first or decline the project.
4️⃣ A — Advance & Protect (Enterprise Perspective)
Security professionals and organizations share responsibility for elevating the profession and maintaining its credibility.
Key Commitments:
Protect professional reputation – avoid harming peers’ standing through malice, careless speech, or unfounded accusations.
Stay current – continuously improve skills, adopt emerging best practices, and adapt to evolving threats.
Mentor generously – share knowledge with juniors, peers, and the wider community to strengthen collective defense.
Example: Anas leads a lunch-and-learn on secure cloud deployment, not because it’s billable, but because raising the team’s skills strengthens Neuromesh’s security culture.
This PAPA model isn’t just a compliance checkbox — it’s a living code of conduct that guides every security decision from incident response to architecture design.
The Neuromesh Analogy
It started when Anya spotted something odd:
The onboarding guide for new devs included entire chunks of code copied from an open-source repo — no attribution, no license check.
Marcus (Security Architect) pointed out that while security hadn’t been breached, IP law had — and legal consequences could be just as damaging.
A week later, Susan from HR emailed Anya asking why the test data for a product demo couldn’t include real customer info. That sparked a GDPR refresher: Just because it’s internal doesn’t mean it’s exempt.
And then Anas (IT Admin) laughed over coffee, “Trade secrets are like the recipe for our Bug Bash Brew — some things you just never share.”
Anya smiled. In security governance meetings, these weren’t just funny anecdotes — they were real guardrails against financial, legal, and reputational collapse.
🧠 Brain Ticklers
Q1:Neuromesh’s fraud detection model is entirely unique and not publicly disclosed. Which form of protection is most appropriate?
A. Copyright
B. Patent
C. Trade Secret
D. Trademark
Q2:A US-based cloud provider selling to federal agencies must follow which program’s controls?
A. ISO 27001
B. FedRAMP
C. SOX
D. CCPA
Q3:Which law enforces healthcare partners to sign BAAs for handling patient data?
A. GDPR
B. HIPAA
C. GLBA
D. PIPEDA
Q4:Which standard ensures cardholder data security during online transactions?
A. NIST CSF
B. PCI DSS
C. COBIT
D. ITIL
Q5:Exporting high-grade encryption software from the US may require review under:
A. HIPAA
B. CCPA
C. Wassenaar Arrangement
D. SOX
Follow the Series : Missed Beginning Read About CIA and Security Governance
