🎯 Concept Focus — Security Policy, Standards, Procedures, Baselines, and Guidelines
When Anya joined Neuromesh, she thought a “policy” was just a dusty PDF in SharePoint.
Marcus, the Security Architect, quickly corrected her:
“A policy is the compass. Standards and baselines are the guardrails. Procedures are the road signs. Guidelines? They’re your driving tips.”
This governance framework translates Neuromesh’s big-picture business goals into day-to-day, enforceable security practices.
Anya realised she’s not here to write every procedure — she’s here to enforce policy and ensure security is woven into daily operations.
Security Policy
Why we need this: It’s part of Neuromesh’s security strategy — capturing the intent of senior management.
Review & Approval: Reviewed annually and approved by the CISO and CIO.
Purpose: Provides an overview of Neuromesh’s security needs and defines strategic objectives, vision, and goals.
Function: Assigns responsibilities, defines roles, specifies audit requirements, outlines enforcement processes, and indicates compliance requirements.
Risk Management: Sets acceptable risk levels for the company.
Mandatory: Non-negotiable for all staff.
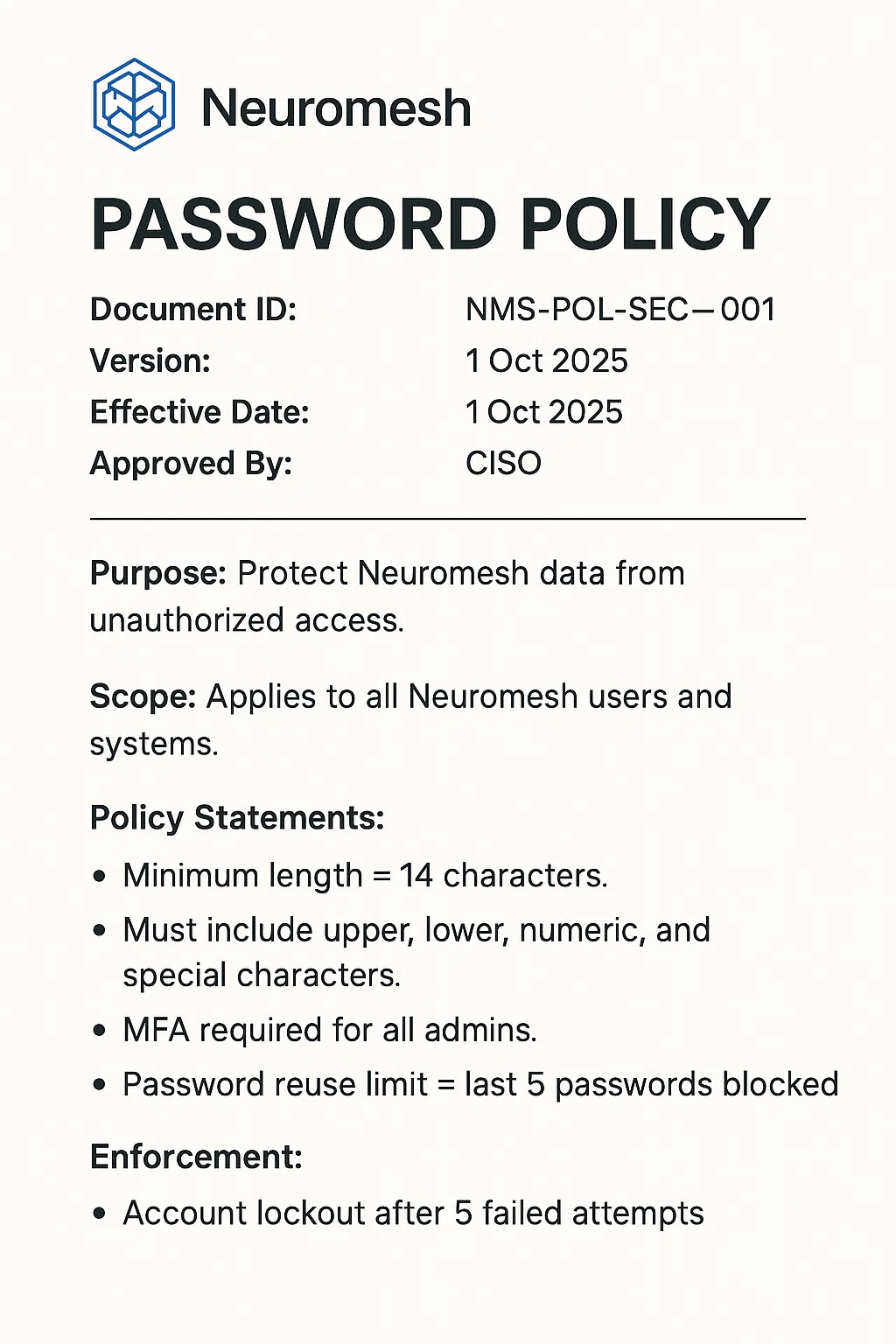
Neuromesh Example:
Password Policy — “All Neuromesh accounts must have a password length ≥14 characters, complexity requirements met, and MFA for privileged accounts.”

Standards
Definition: What’s required to implement the policy.
Nature: Mandatory technical specifications, often hardware or software-specific.
Benefit: Lowers the Total Cost of Ownership (TCO) of safeguards and supports disaster recovery.
Application: Dictates uniformity across departments.
Neuromesh Example:
Secure Email Standard — “All outbound emails containing confidential data must be encrypted using Neuromesh-approved tools.”
Procedures
Definition: Step-by-step, mandatory instructions on how to implement standards and policies.
Goal: Ensures consistent execution and accountability.
Neuromesh Example:
Offboarding Procedure — “Within 15 minutes of employee exit, IT must disable accounts, deactivate building access, and recover Neuromesh-issued devices.”
Baseline
Definition: Uniform method of implementing a standard; sets the minimum acceptable security level.
Nature: Often a technical hardening configuration.
Exceptions: Require senior management sign-off.
Neuromesh Example:
Windows 11 Security Baseline — BitLocker enabled, SMBv1 disabled, account lockout threshold set to 5 attempts.
Guideline
Definition: Recommendations or best practices (optional).
Goal: Aid compliance without enforcing it.
Neuromesh Example:
Workstation Security Guideline — “Use passphrases instead of complex random strings; lock your screen when away.”
Types of Policy
Corporate-Specific: e.g., Neuromesh Enterprise Security Policy
System-Specific: e.g., Neuromesh Cloud Storage Security Policy
Issue-Specific: e.g., Neuromesh Social Media Acceptable Use Policy
Neuromesh Sample Documents
Sample Policy — Password Policy
Sample Standard — Secure Email Standard
All confidential emails must use TLS encryption.
Attachments scanned by DLP before sending.
No personal email accounts for company work.
Sample Baseline — Windows 11 Baseline
Enable BitLocker.
Disable SMBv1.
Require MFA on login.
Sample Procedure — Offboarding
HR notifies IT of exit date.
Disable accounts in AD.
Revoke VPN and application access.
Recover laptops, phones, and badges.
Sample Guideline — New Employee Security Checklist
Use company VPN on public networks.
Avoid storing files locally on laptops.
Report suspicious emails immediately.
🧠 Brain Ticklers
Q1. Neuromesh mandates MFA for all admins in its password policy. Which governance artifact is this?
A. Standard
B. Policy
C. Procedure
D. Baseline
Q2. Neuromesh has a Windows 11 configuration checklist ensuring BitLocker and MFA are enabled. This is:
A. Baseline
B. Guideline
C. Standard
D. Policy
Q3. A document detailing step-by-step actions for disabling accounts during employee offboarding is a:
A. Procedure
B. Standard
C. Policy
D. Baseline
Q4. “Best ways to create strong passphrases” published by Neuromesh with no enforcement is a:
A. Guideline
B. Baseline
C. Standard
D. Policy
Q5. “All confidential emails must be encrypted using TLS” falls under:
A. Guideline
B. Policy
C. Standard
D. Procedure
Follow the Series : Missed beginning Read here
This episode of Anya in Cybersecurity covers Security & Risk Management — part of CISSP Domain 1 preparation. Follow the full series for structured exam readiness.
