Anya had been at Neuromesh barely three weeks when Marcus, the Security Architect, dropped a thick binder on her desk.
Marcus: “This is our risk register. It’s… outdated.”
Anya: “I dont know what that means ?”
🎯 Concept Focus: Risk Management
Risk Terms
Risk Management Process
Risk Terms and Terminologies
Vulnerability – A weakness or lack of an effective control that can be taken advantage of.
Threat – An action, event, or condition capable of exploiting a vulnerability.
Likelihood – Practical probability that a given threat will successfully exploit a vulnerability.
Ask: What are the odds this will occur?
Likelihood can be reduced when appropriate controls are introduced.
Impact – The magnitude of harm if the event occurs (financial, legal, operational, reputational).
Risk – Combination of likelihood and impact.
Working formula: Risk = Likelihood × Impact
The OWASP Risk Rating Model is a common approach to structure these inputs.
Exposure – Portion of asset value expected to be lost if the event happens.
Threat Agent – The actor (human, system, process) carrying out the attack.
Safeguard – Preventive, proactive control (e.g., strong passwords, MFA).
Countermeasure – Corrective, reactive measure (e.g., isolate an infected workstation).
Due Care – Taking reasonable, prudent protective actions (“do the right things”).
Due Diligence – Maintaining those protections over time (“keep doing the right things”).
Risk Policy – The organization’s formal statement of risk management objectives and expectations.
Ownership note: The asset owner determines value, mandates safeguards and countermeasures, and is accountable for risk reduction decisions.
Risk – The combination of likelihood and impact.
Formula: Risk = Likelihood × Impact

The Risk Management Process (5 stages)
1. Risk Identification
2. Risk Analysis
3. Risk Evaluation
4. Risk Treatment
5. Monitoring & Review
Image Courtesy : Risk Mangement Mind Map DestCert
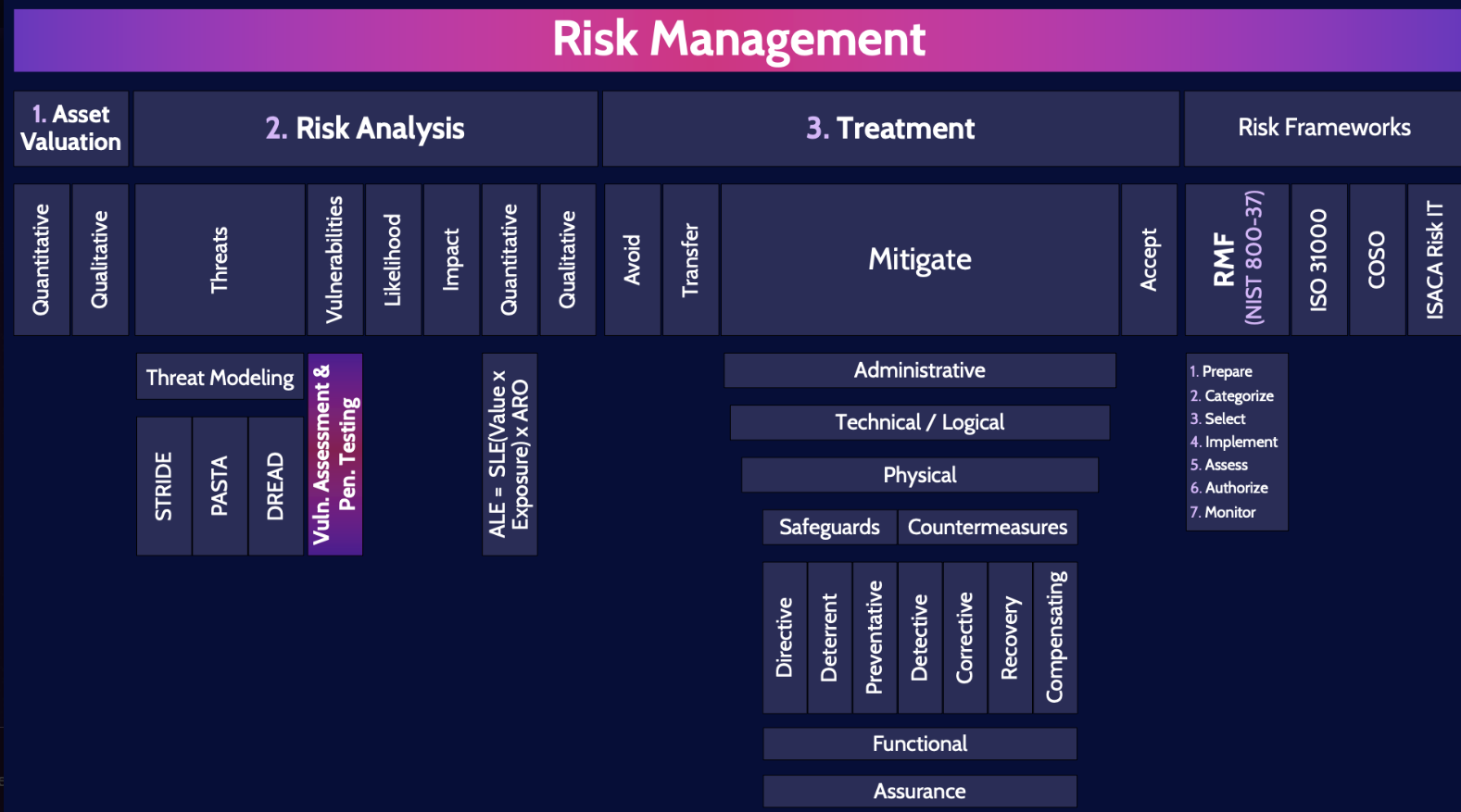
1) Risk Identification
Purpose: discover what could go wrong and where.
1.1 Asset Valuation
Who: Asset Owners, System Owners, Data Stewards, Business Process Owners; facilitated by Risk Analysts/GRC, with input from Finance and IT Ops.
How:
Build/refresh the asset inventory (systems, data sets, services, facilities, third‑party services).
Establish ownership and custodianship, dependencies, and locations.
Classify data and systems (e.g., confidentiality/integrity/availability levels).
Assign value using a mixture of: replacement cost, revenue at risk, regulatory penalty exposure, operational downtime cost, and reputational sensitivity.
Outputs/Artifacts: Asset register with owner, classification, criticality, dependencies, location, and valuation notes.
1.2 Threat Analysis
Who: Risk Analysts, Security Architecture/Operations, Threat Intel.
How: Identify threat sources (internal, external, partners, natural, accidental), threat events, and applicable TTPs. Use catalogs and prior incidents to enumerate realistic scenarios.
Outputs: Threat library mapped to assets/processes, with rough likelihood cues.
1.3 Vulnerability Assessment
Who: Security Engineering/Operations, AppSec, Infra teams; sometimes external assessors.
How: Configuration reviews, vulnerability scans, code analysis, architecture reviews, and manual testing to surface weaknesses exploitable by identified threats.
Outputs: Vulnerability findings tied to specific assets, with severity, exposure context, and remediation candidates.
2) Risk Analysis
Purpose: convert raw findings into decision‑ready numbers or scores.
Qualitative Analysis – Fast, subjective triage using bands like High/Medium/Low for likelihood and impact. Good for quick prioritization.
Semi‑Qualitative Analysis – Use numeric scales with categories (e.g., Likelihood 1–5, Impact 1–5) and sum or multiply to derive a risk score.
Quantitative Analysis – Express in numbers/currency for items with sufficient data, focusing on high‑probability, high‑impact cases. Use:
AV (Asset Value),
EF (Exposure Factor),
SLE (Single Loss Expectancy),
ALE (Annual Loss Expectancy),
ARO (Annualized Rate of Occurrence; default 1 if none stated).
Formulas:
SLE = AV × EF
ALE = SLE × ARO
Evaluate safeguard economics with ACS (Annual Cost of Safeguard):
ACS = (ALE_before − ALE_after) − Safeguard_Cost
Outputs: Risk register entries with likelihood, impact, chosen analysis method, calculations, and assumption notes.
3) Risk Evaluation
Purpose: decide what the numbers mean against organizational thresholds.
Risk Capacity – Upper bound of risk the enterprise can sustain without imperiling viability. If required tolerance exceeds capacity, the correct posture is avoidance (proactive).
Risk Tolerance – The explicit, measurable limit per asset–threat pair that defines what is acceptable.
Risk Appetite – The aggregate level of risk leadership is willing to shoulder across the portfolio.
Outcome: Each risk is tagged above/below tolerance, which drives treatment choice.
4) Risk Treatment
Purpose: modify risk so it fits within tolerance.
Definition: Selecting and implementing measures to change likelihood and/or impact.
Four categories:
Avoid – Eliminate the exposure by not doing the risky activity or replacing it with a safer alternative.
Transfer – Shift financial exposure or operational responsibility (e.g., insurance, outsourcing) while keeping accountability.
Accept/Retain – Live with the risk when business value > risk, the risk is below appetite, or the cost of controls exceeds the benefit; budget accordingly.
Mitigate/Reduce – Implement controls to lower likelihood/impact to within tolerance. The risk that remains after controls is residual risk.
Essential Terms
Inherent Risk – Risk before any controls.
Residual Risk – Risk after controls. It can be accepted (if within tolerance), transferred (e.g., insurance), or monitored continuously.
Control Risk – Risk introduced by the control environment itself (e.g., misconfigurations, failure modes).
Clarification on residual risk:
Correct: “Residual risk is the risk after implementing controls.”
Nuance: Management may accept it if within tolerance; otherwise they can transfer or continue to treat/monitor.
Better phrasing: Residual risk is the remaining exposure after controls. If that exposure is within tolerance, management may choose acceptance rather than further mitigation.
5) Monitoring, Review, and Governance Alignment
Purpose: ensure controls remain effective and risks don’t drift.
NIST SP 800‑37 RMF phases to anchor governance:
Categorize information systems (FIPS 199 / SP 800‑60).
Select security controls (FIPS 200 / SP 800‑53).
Implement selected controls.
Assess control effectiveness (SP 800‑53A).
Authorize system operation based on residual risk.
Monitor controls and environment continuously.
Artifacts: Continuous risk register updates, KRI dashboards, assessment reports, ATO/POA&M updates.
Security Controls: What to Weigh
When choosing countermeasures, consider:
Security effectiveness (does it reduce risk meaningfully?).
Cost effectiveness (ALE reduction vs. cost).
Operational impact (latency, usability, maintainability).
Implementation essentials
Maintain clear documentation of work by platform/area and communicate progress to management.
Keep a live inventory of controls mapped to specific risks.
Apply strong access control to the documentation itself (prevent unauthorized access/changes/leaks).
Controls Catalog
Types
Physical – Barriers and devices (locks, guards, cameras).
Administrative/Managerial – Policies, procedures, training, background checks.
Technical/Logical – Security tech (firewalls, encryption, MFA).
Categories (use across the incident timeline)
Directive – State required behaviors.
Deterrent – Make malicious behavior less attractive.
Preventive – Stop the action from occurring.
Compensating – Reduce risk when primary controls are not feasible or fail.
Detective – Reveal hostile or anomalous activity.
Corrective – Remediate after an event.
Recovery – Restore to known-good operation.
Control Assessment and Testing
SCA (Security Control Assessment) – Formal, often external evaluation; evidences compliance and enforcement.
CSA (Control Self‑Assessment) – Internal, self‑driven evaluation of risks, controls, and processes to find and close gaps.
Effectiveness assessment methods
Vulnerability Assessment
Penetration Testing (with explicit authorization, since it may impact CIA):
Internal (inside network), External (perimeter/external assets).
Blind (red team limited knowledge; blue aware a test is on).
Double‑blind (red with no prior knowledge; blue not informed).
By tester knowledge
Black‑box (Zero knowledge)
Gray‑box (Partial knowledge)
White‑box (Full knowledge)
Four‑stage PT flow
Planning – Scope, goals, rules of engagement.
Discovery – Intel gathering, scanning, attack‑path identification.
Attack – Exploit safely to test defenses.
Reporting – Findings, risk ratings, remediation guidance.
Other methods
DoS testing (availability focus), war dialing, war driving, social engineering, pivoting (move from one network segment to another).
Traffic padding – Not a pen‑test technique (don’t confuse it).
Attack Progression Reference
Lockheed Martin Cyber Kill Chain – Detect early, break the chain, and design effective controls.
Reconnaissance
Weaponization
Delivery
Exploitation
Installation
Command & Control
Actions on Objectives
Threat Modeling
Best done in design; also revisit at major changes.
Process: Identify threats → Diagram attack paths → Reduction analysis → Prioritize and respond.
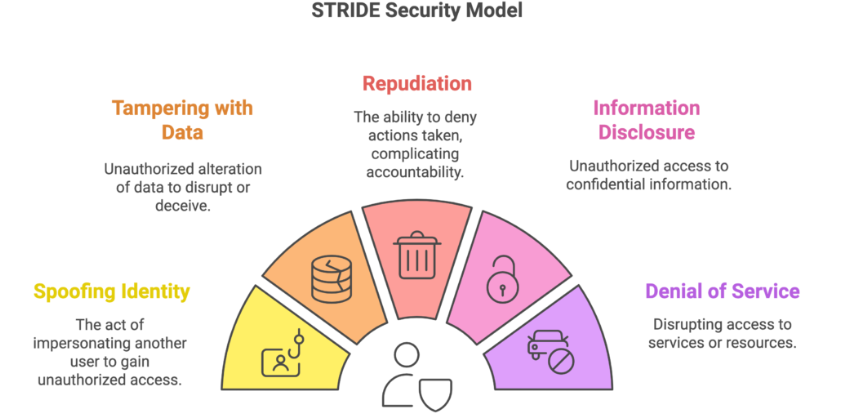
STRIDE – Threat classes and common mitigations
Spoofing (AuthN) → MFA, certificates, biometrics
Tampering (Integrity) → Integrity checks, digital signatures, secure transport (HTTPS)
Repudiation (Non‑repudiation) → Logging, auditing, non‑repudiation tools
Information Disclosure (Confidentiality) → Encryption, masking, access control
Denial of Service (Availability) → Rate limiting, redundancy, firewalls/filters
Elevation of Privilege (Authorization) → Least privilege, patching, RBAC
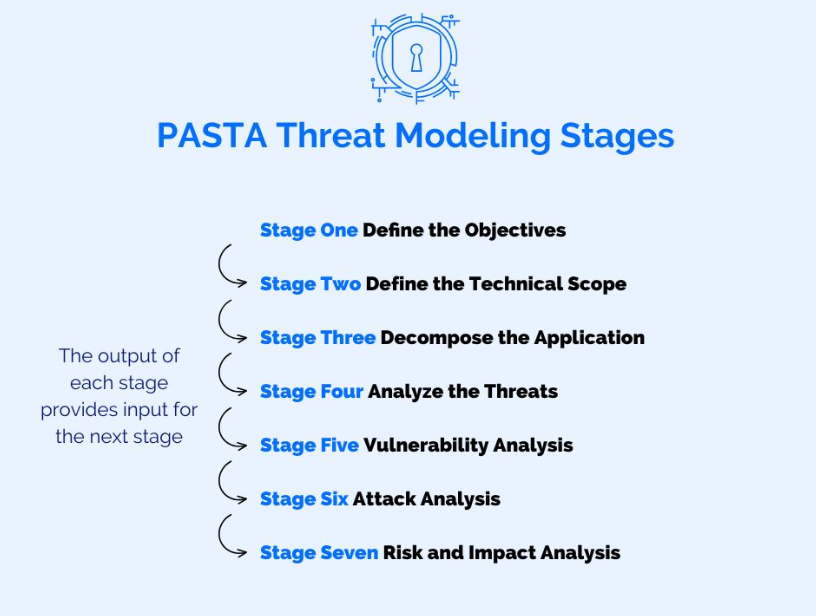
PASTA – Seven‑step Process for Attack Simulation & Threat Analysis, aligning business objectives and technical requirements, including compliance.
DREAD – Prioritization model scoring Damage, Reproducibility, Exploitability, Affected users, Discoverability (each typically 1–10).Use STRIDE to identify what threats exist; use DREAD to determine which pose the greatest business risk.
Physical & Human‑centric Threats
Infrastructure disruption/destruction –
Tailgating (no consent)
Piggybacking (with consent)
People compromise –
Social engineering, phishing, pretexting, baiting
Supply Chain Risk Management
Applies to both physical and digital products/services.
What to check
Use trusted vendors/suppliers.
Ensure goods are authentic and free of malicious alteration.
Test and verify against clear security standards.
Reviews and evidence
Governance (policies/procedures), site security, formal audits (SOC 2, ISO reports), penetration testing.
Useful reports
ISO‑certified audits, CSA STAR, AICPA SSAE‑16 SOC series.
Common risks
Product tampering, counterfeits, implants.
Mitigations
Silicon Root of Trust (RoT) – Ensures integrity, authenticity, confidentiality of the boot chain and platform software.
Physically Unclonable Function (PUF) – Hardware fingerprints to prevent counterfeits.
SBOM (Software Bill of Materials) – Transparency of components to find known vulnerabilities and patch promptly.
Acquisition strategy
Perform risk management as part of acquisition for all external products/services.
Maintain a supply‑chain policy (or embed its requirements into the acquisition policy).
Ongoing third‑party assessment
On‑site assessments, document exchange, policy/process reviews.
Service agreements
For every service, define:
SLR (Requirements) – What the customer needs.
SLA – What both parties commit to (include service metrics and right to audit).
Review annually; one SLA may cover multiple services.
SLR (Report) – How well the provider performed.
OLA – Internal SLA between business units; review regularly (e.g., weekly).
🧠 Brain Ticklers
Q1: Marcus is debating whether to patch a vulnerability now or after the product launch. The vulnerability poses medium likelihood but high impact. Which treatment aligns best if the residual risk exceeds tolerance?
A. Accept
B. Transfer
C. Mitigate
D. AvoidQ2:Neuromesh’s finance team sets a €500k risk appetite for a new AI project. The board agrees tolerance is €550k. A risk is estimated at €600k. What’s the correct decision?
A. Proceed without change
B. Reduce likelihood or impact
C. Accept residual risk
D. Avoid due to exceeding capacityQ3:If Neuromesh implements network segmentation to contain IoT breaches, what type of control is this?
A. Physical
B. Administrative
C. Technical
D. RecoveryQ4:During a third-party audit, a vulnerability remains after controls are in place. What is this known as?
A. Control Risk
B. Inherent Risk
C. Residual Risk
D. Tolerance BreachQ5:Which RMF phase formally accepts the residual risk and authorizes the system to operate?
A. Implement
B. Authorize
C. Select
D. MonitorFollow the Series : Missed beginning Read here
Concept in briefThis episode of Anya in Cybersecurity covers Security & Risk Management — part of CISSP Domain 1 preparation. Follow the full series for structured exam readiness.
